cATO Bridge
It’s time to automate the manual burden of continuous authority to operate (cATO).

Goodbye “check-the-box” culture. Hello, automated continuous authorization. 👋
If you've been through the authority to operate (ATO) process, you already know the struggle: Months of manual effort. A 400-page system security plan that's already stale the day it's signed. Repeat in three years.
Continuous ATO (cATO) has become the obvious answer, but almost no one has a clear path to actually getting there. Some teams are getting 20–50% control inheritance through their cloud service provider (CSP) and governance, risk, and compliance (GRC) platform. And, that's a real starting point — but it still leaves the majority of the work on your ISSOs.
Aquia cATO Bridge gets you to nearly 80% control inheritance and changes your ATO process from a documentation exercise into real-time risk reduction.
78%
Control inheritance
6 weeks
time to initial ATO (vs. the standard 12-18 months)
$4M
in savings for a large federal agency
74%
Reduction in compliance overhead
What is Aquia cATO Bridge?
cATO Bridge is an OSCAL-native compliance automation engine that replaces the static document cycle with a living, automated, real-time picture of your security posture.
It works by connecting directly to your existing cloud environment — pulling raw data from your CI/CD pipeline, cloud infrastructure, and security tools — and normalizing it into control evidence that flows automatically into your GRC platform of choice. No manual translation. No stale snapshots.
Teams that used to spend 12–18 months on their initial ATO are doing it in weeks.
How cATO Bridge Automates Continuous Compliance
cATO Bridge uses API-based integrations and automations to connect your cloud environment to the GRC tools your teams already use — normalizing raw compliance data, mapping it to NIST 800-53 controls, and routing it to your GRC platform of choice.
-
Built on services already approved in your environment (for example, AWS Audit Manager, Config, and Security Hub), so there's nothing new to procure or authorize.
-
Raw data from your CI/CD pipeline, cloud infrastructure, and security tools is normalized and mapped to the controls that matter, without manual translation.
-
Whether you're using CSAM, ServiceNow, Archer, RegScale, or another GRC platform, cATO Bridge formats and routes your compliance data to the appropriate formats required for documentation import and export.
-
Real-time leadership-ready posture visibility across systems, so ISSOs, assessors, and authorizing officials have the data they need when they need it.
See cATO Bridge in Action
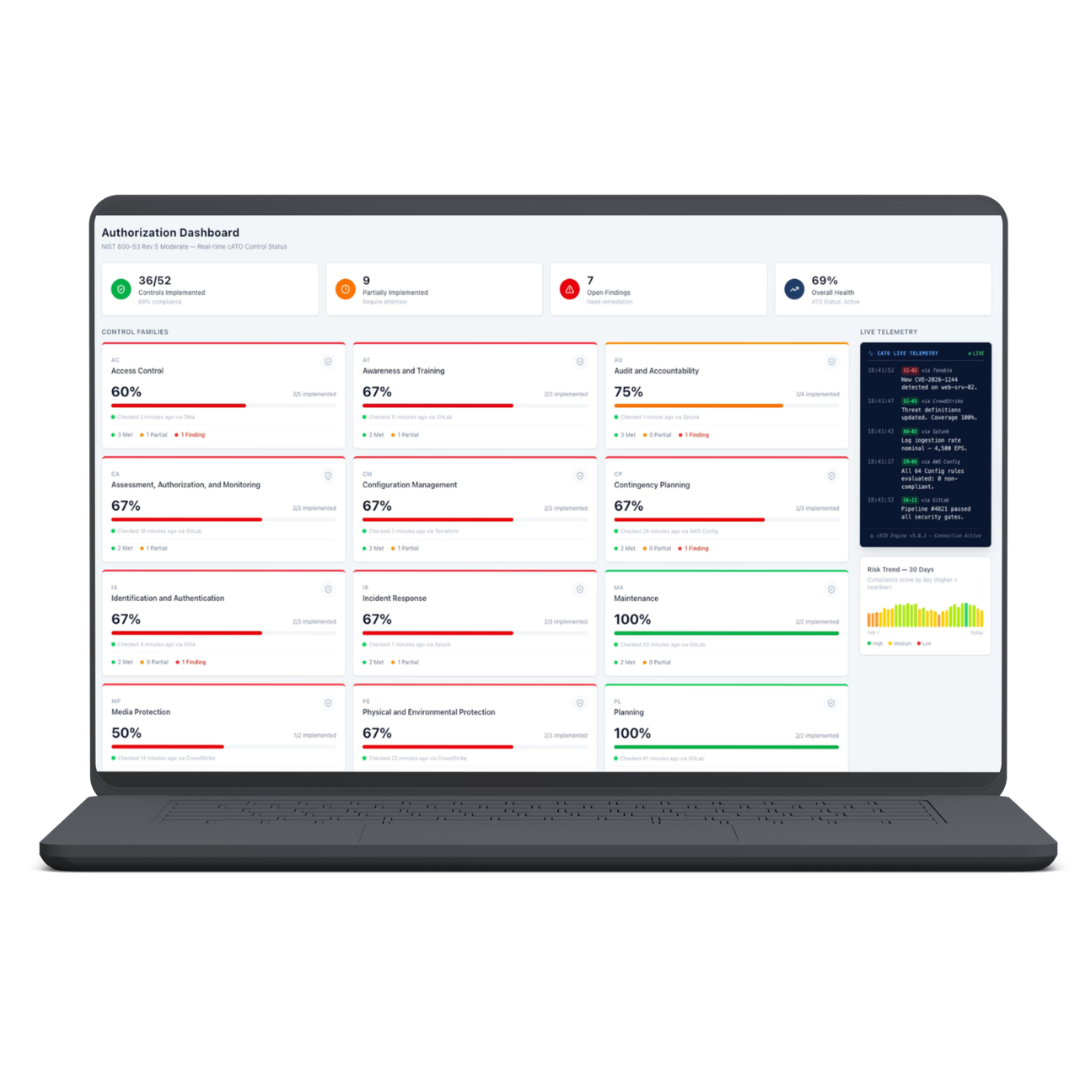
Our demo walks you through the real-time authorization dashboard, control family cards, automated plan of action and milestones (POAM) generation, and system security plan (SSP) generation.
Request a Consultation
“I already have a GRC tool. Why do I need cATO Bridge?”
cATO Bridge is the automation between your cloud service provider (CSP) services and your GRC platform.
Federal compliance has a data problem. Agencies run dozens of cloud systems that generate enormous amounts of security and audit data, but it arrives in inconsistent formats, from different tools, and at different cadences. Translating that raw data into control evidence has historically been a manual, error-prone task that has fallen to ISSOs.
cATO Bridge is the layer that fixes this. Think of it as a water filtration system: your cloud environment generates the raw data, and cATO Bridge filters, normalizes, and routes it so it can flow cleanly into whichever GRC tool you're using.
Your compliance pipeline becomes automated. Your ISSOs shift from translating data to reviewing findings. And your assessors go from working one system per month to monitoring dozens on an ongoing basis.
Free Resource
Download a copy of our white paper, “cATO+ and Federal Compliance Modernization: Accelerating Continuous Authority to Operate Through Compliance Documentation Automation.”
We’re in good company.
Work With Us
GSA Schedule and SINS
GSA Schedule 47QTCA23D000H
SIN 518210C Cloud Computing and Cloud
SIN 54151HACS Highly Adaptive Cybersecurity Services (HACS)
SIN 54151S Information Technology Professional Services
Federal Contract Vehicles
USDA STRATUS Cloud BOA
VA SPRUCE IDIQ
Company Profile
CAGE Code: 8XPQ4
DUNS: 117948867
Unique Entity ID: RGMQQK1DLAN9
NAICS Codes
541511 Custom Computer Programming Services (primary)
334111 Electronic Computer Manufacturing
334112 Computer Storage Device Manufacturing
334310 Audio And Video Equipment Manufacturing
334419 Other Electronic Component Manufacturing
518210 Data Processing, Hosting, And Related Services
519130 Internet Publishing And Broadcasting And Web Search Portals
519190 All Other Information Services
541430 Graphic Design Services
541512 Computer Systems Design Services
541513 Computer Facilities Management Services
541519 Other Computer Related Services
541611 Administrative Management And General Management Consulting Services
541614 Process, Physical Distribution, And Logistics Consulting Services
541618 Other Management Consulting Services
541715 Research And Development In The Physical, Engineering, And Life Sciences (Except Nanotechnology And Biotechnology)
561110 Office Administrative Services
561320 Temporary Help Services
561439 Other Business Service Centers (Including Copy Shops)
611420 Computer Training
Partnerships
AWS Advanced Tier Services Partner
AWS Public Sector Partner
AWS Global Security and Compliance Acceleration program (ATO on AWS)
AWS Security Partner
GCP Partner
Membership
Digital Services Coalition
National Veteran Small Business Coalition (NVSBC)


Stay in the Know
Sign up to receive updates.